Three Main Areas in Security Awareness Training

The three main areas in security awareness training are phishing and social engineering recognition, password and credential security, and data protection and safe device use. These three areas cover the core human behaviors that attackers exploit most often. According to Verizon's 2025 Data Breach Investigations Report, 60% of all data breaches now involve a human element. Training employees in these three areas is the most direct way to reduce that risk.
This guide breaks down each area in depth. We also cover what good training looks like, how to measure whether it is working, which security principles and frameworks guide the best programs, and how to build a security culture that actually sticks.
What Should Security Awareness Training Include?
Security awareness training should include phishing recognition, social engineering defense, password hygiene, data handling practices, safe device use, and incident reporting procedures. These topics address every major category of human-driven security failure that attackers rely on.
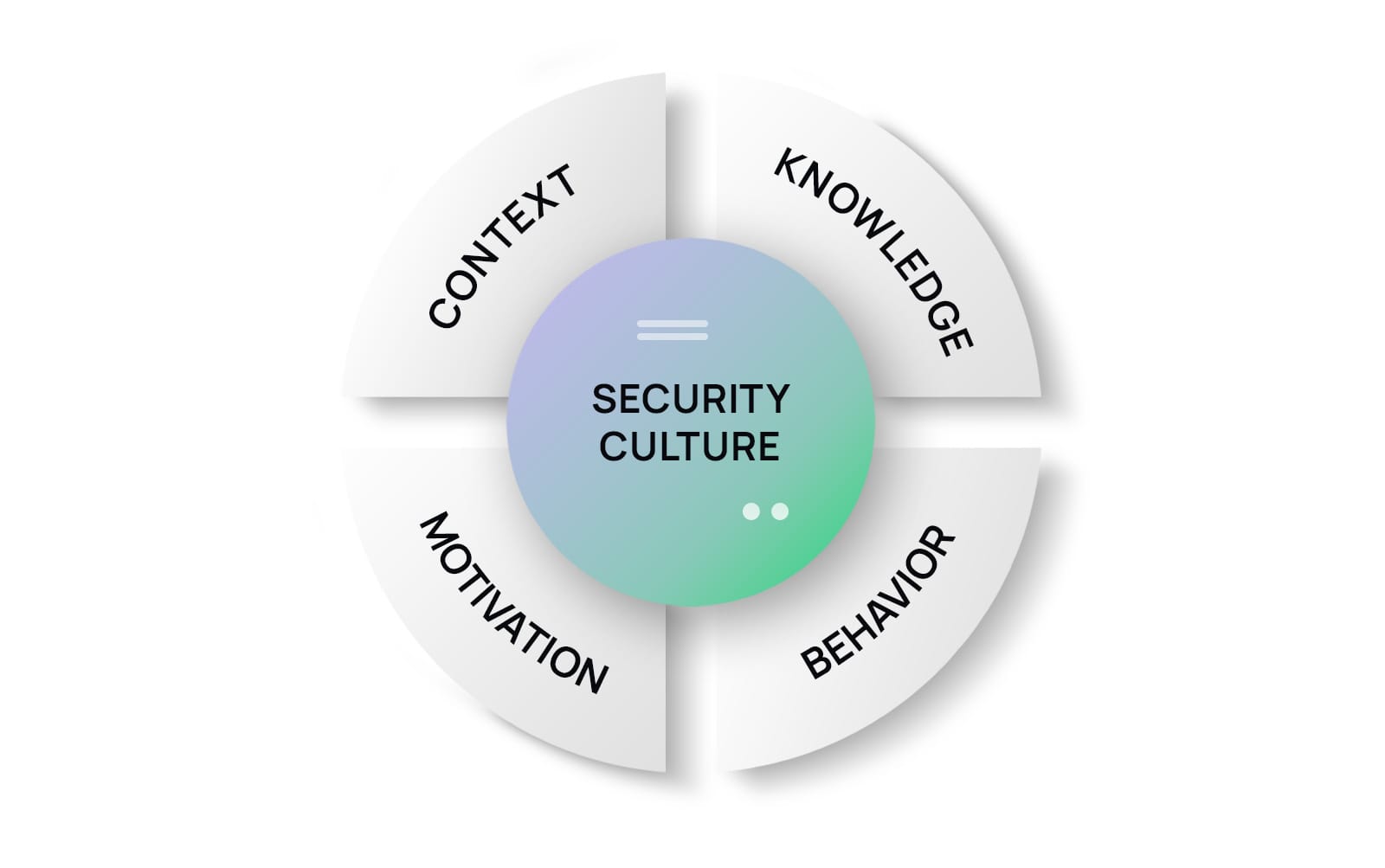
The goal is not just to teach employees facts. The goal is to change behavior. According to the 2025 Fortinet Security Awareness and Training Report, 67% of decision makers say their employees still lack basic security awareness, even at organizations that already run training programs. That gap exists because most programs focus on one-time instruction rather than continuous, behavior-based reinforcement.
A complete program covers what to look for, what to do when something looks wrong, and how to report it. It uses real-world simulations, not just slide presentations. And it repeats those lessons regularly, because according to IBM research, only 10% of employees retain what they learned in annual training after just three months.
What Are the Three Main Areas in Security Awareness Training?
The three main areas in security awareness training are phishing and social engineering recognition, password and credential security, and data protection with safe device use. Each area targets a different category of human vulnerability that cybercriminals exploit every day.
Area 1: Phishing and Social Engineering Recognition
Phishing and social engineering recognition is the first and most critical area in security awareness training because these attacks are the starting point for the vast majority of breaches. According to the 2025 KnowBe4 Phishing by Industry Benchmarking Report, 33.1% of untrained employees click on simulated phishing emails. That means roughly one in three people in an untrained workforce will fall for a convincing fake email.
Phishing is a type of social engineering. It uses deceptive emails, text messages, or websites to trick people into revealing credentials, clicking malicious links, or sending money. Social engineering is the broader category, which includes phone-based attacks called vishing, text-based attacks called smishing, and impersonation scams where an attacker pretends to be a trusted person like an IT staffer or executive.
What makes these attacks so effective is that they target human psychology, not technology. Attackers create a sense of urgency, fear, or authority that bypasses careful thinking. A fake email that appears to come from the CEO asking for an immediate wire transfer does not need to bypass a firewall. It just needs one employee to act before they think.
Training in this area teaches employees to recognize warning signs: unexpected requests for credentials or money, mismatched sender addresses, grammar that does not match a brand's normal style, and pressure to act quickly without verification. It also teaches the correct response, which is to pause, verify through a known channel, and report the attempt to IT. Different types of cyber attacks all trace back to this human entry point.
The good news is that this area is also the most trainable. According to KnowBe4's research, organizations that run ongoing security awareness training reduce phishing susceptibility by over 40% within just 90 days and by up to 86% within a year. That is a dramatic improvement from a relatively simple investment.
Area 2: Password and Credential Security
Password and credential security is the second main area in security awareness training because stolen or weak credentials are involved in nearly every major attack chain. According to the Verizon 2025 DBIR, credential abuse accounted for 22% of initial access vectors in breaches analyzed that year. Once an attacker has valid credentials, they can move through a network quietly, appearing to be a legitimate employee.
This area covers three core behaviors. First, employees need to use strong, unique passwords for every account. A strong password is at least 12 characters long and mixes letters, numbers, and symbols. Reusing the same password across accounts means one compromised site gives attackers access to everything else. According to Infrascale's 2025 Security Awareness Training Report, password reuse is identified as a persistent gap by 45% of senior technology leaders surveyed.
Second, employees need to use a password manager. Password managers generate and store unique passwords for every account, so employees only need to remember one master password. This removes the practical excuse for reusing passwords and dramatically reduces the chance of a credential-based breach.
Third, multi-factor authentication must be part of every employee's daily login process. MFA requires a second proof of identity beyond the password, such as a code sent to a phone or generated by an authenticator app. Even if a password is stolen through a phishing attack, MFA blocks the attacker from using it. Our existing blog on MFA vs. 2FA authentication explains how these layers work together.
Area 3: Data Protection and Safe Device Use
Data protection and safe device use is the third main area in security awareness training. It covers how employees handle sensitive information, how they use their devices, and what they do when something goes wrong. This area matters because not all security breaches are caused by clever attacks. Many happen because an employee sent a file to the wrong person, left a laptop in a car, or connected to an unsecured Wi-Fi network without a VPN.
Training in this area teaches employees to classify data correctly. Not every file carries the same risk. A marketing brochure and a client's financial records are very different things, and employees need to treat them differently. Sensitive data should never be sent over personal email, stored on personal devices without authorization, or shared with people who do not need it for their job.
Safe device use covers physical security and digital hygiene. Screens should lock automatically after a short period of inactivity. Devices should have encryption enabled. Software updates should be applied promptly because unpatched software is one of the most common ways attackers gain entry. According to a 2025 report from Keepnet, over 36% of employees using personal devices for work admit to postponing security updates.
This area also includes what to do when a device is lost or stolen. Employees need to know who to call immediately and understand that quick reporting enables remote wiping of the device before data can be accessed. Fast action in those first hours makes the difference between a minor incident and a full breach. Our team helps businesses in Huntsville and across North Alabama set up the systems that make this kind of fast response possible, including BYOD security practices for mixed device environments.
What Are the Three Main Security Objectives?
The three main security objectives are confidentiality, integrity, and availability, often called the CIA triad. These three objectives are the foundation of every security framework, including the ones that govern security awareness training.
Confidentiality means that sensitive information is only accessible to people who are authorized to see it. Phishing attacks and credential theft directly threaten confidentiality by giving unauthorized people access to data they should never reach. Integrity means that data is accurate and has not been altered without authorization. Social engineering attacks like business email compromise threaten integrity by tricking employees into changing payment details or account information based on fake instructions. Availability means that systems and data are accessible when legitimate users need them. Ransomware, which often starts with a phishing email, directly attacks availability by locking files and demanding payment to restore access.
Security awareness training protects all three objectives simultaneously. When employees stop phishing attacks, they protect confidentiality. When they verify unusual requests before acting, they protect integrity. When they recognize and report ransomware early, they protect availability. This is why employee training is not just a compliance checkbox but a direct business protection strategy.
What Are the Three Core Principles of Security?
The three core principles of security are the CIA triad: confidentiality, integrity, and availability, as described above. These principles apply equally to physical security, network security, and human security. A training program built around these three principles gives employees a mental framework they can apply to any situation, even ones they have never specifically trained for. If an action puts confidential data at risk, or could change important records without authorization, or could lock a system down, it is a security concern worth reporting.
What Are the Three Basic Security Concepts?
The three basic security concepts are threat, vulnerability, and risk. A threat is something that could cause harm, like a hacker attempting to steal data. A vulnerability is a weakness that a threat could exploit, like an employee who has not learned to recognize phishing emails. Risk is what you get when a threat meets a vulnerability: the likelihood and potential impact of something going wrong. Security awareness training directly reduces vulnerability, which in turn reduces risk even when the same threats remain active. This is why well-designed training programs are one of the highest-return investments in a security budget.
What Are the Three Pillars of Security?
The three pillars of security are people, processes, and technology. Security awareness training addresses the first pillar directly, but all three must work together for a complete defense.
People are both the greatest risk and the greatest asset in any security program. According to a 2024 study by Mimecast, human error contributed to 95% of data breaches that year. But the same research also shows that organizations with strong training programs can reduce their susceptibility to phishing attacks by up to 86% within a year. People can be trained to be your best line of defense rather than your biggest weakness.
Processes are the documented rules and procedures that tell people what to do in specific situations. A clear incident reporting process means employees know exactly who to call when they see something suspicious. A data classification policy tells employees how to handle different types of information. Without clear processes, even well-trained employees may not know what the right action is. Developing a solid incident response plan for your business is one of the most important process steps you can take.
Technology supports people and processes but cannot replace them. Firewalls, email filters, endpoint protection tools, and monitoring systems all add important layers of defense. But technology alone cannot stop a motivated attacker from sending a convincing email to an employee who does not know how to recognize it. All three pillars must be in place and working together. We help businesses build this complete picture through our complete compliance and security services.
What Are the 5 Basic Principles of Security?
The 5 basic principles of security are confidentiality, integrity, availability, authentication, and non-repudiation. The first three form the CIA triad already discussed. Authentication is the process of verifying that a user is who they claim to be, which is why password training and MFA are so important. Non-repudiation means that actions can be traced back to the person who performed them, so no one can deny sending a particular message or making a specific change to a system. Audit logs and activity monitoring support non-repudiation. Security awareness training connects to all five principles by teaching employees to protect data, verify identities, report incidents, and use systems in ways that leave a traceable record.
What Are the 3 P's of Security?
The 3 P's of security are prevention, protection, and prosecution. Prevention is about stopping attacks before they happen, which is exactly what security awareness training does. Protection means having the right tools and processes in place to limit damage when an attack does get through. Prosecution refers to the documentation, logging, and evidence-gathering that supports legal action or disciplinary procedures after a breach. Training supports all three P's by making employees active participants in each stage, not passive bystanders.
What Are the 5 C's in Security?
The 5 C's in security are change, compliance, cost, continuity, and coverage. Change refers to keeping systems updated and adapting to new threats. Compliance means meeting the regulatory and legal requirements that govern your industry. Cost involves managing security expenditures in a way that delivers real protection without overspending. Continuity means keeping business operations running even after a security incident. Coverage means ensuring that every part of your environment, including people, is protected. Security awareness training touches every one of these: it adapts to new threats, supports compliance, delivers a strong return on investment, helps minimize downtime from breaches, and ensures that human behavior is covered as part of the overall security strategy.
Security Awareness Training: Key Program Elements Compared
Training ElementWhat It AddressesDelivery MethodProven ImpactPhishing SimulationsPhishing and social engineering recognitionSimulated fake emails with immediate feedbackReduces click rate from 33% to under 5% within 12 months (KnowBe4, 2025)Password Hygiene ModulesCredential security and MFA adoptionInteractive e-learning, policy enforcementCredential abuse involved in 22% of breach initial access vectors (Verizon DBIR, 2025)Data Handling TrainingData classification, safe sharing, device securityRole-based modules, scenario exercises36% of employees delay security updates without training reinforcement (Keepnet, 2025)Social Engineering AwarenessVishing, smishing, pretexting, CEO fraudVideo scenarios, live-fire drillsSocial engineering initiates 30%–41% of all successful attacks (Verizon DBIR, 2025)Incident Reporting ProceduresWhat to do and who to call after spotting a threatPolicy training, tabletop exercisesWell-trained employees report 3–5x more suspicious emails (Keepnet, 2025)
Sources: KnowBe4 Phishing by Industry Benchmarking Report 2025; Verizon Data Breach Investigations Report 2025; Keepnet Security Awareness Training Statistics 2026; Infrascale Security Awareness Training USA 2025.
What Are the Three Areas of Security?
The three areas of security are physical security, technical security, and administrative security. Physical security protects the buildings, equipment, and people inside them. Technical security covers the software and hardware tools like firewalls, endpoint protection, and encryption. Administrative security encompasses the policies, procedures, and training programs that govern how people behave within a security framework.
Security awareness training sits squarely in administrative security, but it has ripple effects across all three areas. An employee who knows to challenge an unfamiliar person in a secure area is supporting physical security. An employee who knows not to plug in an unknown USB drive is supporting technical security. An employee who knows how to handle a data request from an unverified source is supporting administrative security. All three areas connect through the behavior of your people.
For regulated businesses, all three areas must also satisfy compliance requirements. HIPAA requires both technical safeguards and training for anyone who handles patient data. CMMC requires administrative controls including documented security awareness training for all personnel who access covered systems. PCI DSS requires organizations to educate personnel about information security policies and procedures annually. Our team supports healthcare organizations and other regulated industries in building training programs that satisfy these specific requirements.
What Are the Three Major Areas of Security?
The three major areas of security are operational security, information security, and physical security. Operational security, often called OPSEC, focuses on protecting sensitive processes and data from being observed or exploited by adversaries. Information security focuses on protecting data in all its forms, whether stored, transmitted, or processed. Physical security protects facilities, equipment, and personnel from direct, in-person threats. Security awareness training is essential to all three because human behavior is the variable that ties each area together. A well-trained employee protects operations by not oversharing, protects information by handling data correctly, and supports physical security by following access procedures.
What Is the Most Important Security Awareness Training Topic?
The most important security awareness training topic is phishing recognition. According to Fortinet's 2024 Security Awareness and Training Report, 53% of US senior technology leaders say phishing is the threat employees are least prepared to handle. This gap matters because phishing is also the most common attack vector: it starts roughly 30% to 41% of all successful breaches according to Verizon's research.
Phishing is the gateway. Once an employee clicks a malicious link or hands over their credentials to a fake login page, every other security control is at risk. Firewalls cannot stop data being sent out by a logged-in user. Endpoint protection may not catch a credential being typed into a spoofed website. Only the employee, in that moment, stands between the attacker and access.
This is exactly why phishing simulations are the highest-impact single tool in a training program. They give employees safe, repeated practice at recognizing attacks under realistic conditions. When a real attack comes, the response has become almost automatic. That muscle memory is what protects organizations day after day. We cover the broader landscape of small business cybersecurity misconceptions that often prevent companies from taking this step seriously.
What Is General Security Awareness Training?
General security awareness training is a foundational program that covers the core cybersecurity topics every employee needs to know, regardless of their job role. It typically includes phishing recognition, password security, data handling basics, safe internet use, and how to report security incidents. General training is the starting point for all employees, usually delivered during onboarding and refreshed annually. It contrasts with role-based training, which goes deeper on the specific threats relevant to a particular job function, such as wire fraud defense for finance staff or medical record handling for clinical teams. Both types are needed: general training builds the baseline, and role-based training addresses the higher-risk behaviors specific to each team.
What Is the Basic Security Awareness Training BSAT?
BSAT stands for Basic Security Awareness Training and refers to a standardized, mandatory training program that covers the minimum cybersecurity knowledge every employee should have. In federal government and defense contracting contexts, BSAT is often required as a documented compliance control. It covers core topics including recognizing social engineering, handling sensitive data, password security, and incident reporting. For defense contractors operating under CMMC requirements, completing and documenting BSAT for all personnel who access covered systems is a required control. We regularly help government contractors in the region build and document these programs as part of their government compliance work.
What Are the Three Main Steps to Implementing Security Awareness?
The three main steps to implementing security awareness are assess, train, and measure. Every effective security awareness program follows this cycle, and it never fully stops because the threat landscape keeps changing.
Step 1: Assess. Before training begins, you need to know where the gaps are. A baseline phishing simulation shows what percentage of your employees click on fake emails before any training. A risk assessment identifies which departments handle the most sensitive data and which job functions face the highest threat exposure. According to the 2025 Fortinet report, 34% of organizations say personnel limitations were the main reason they delayed implementing training, but a baseline assessment does not have to be complex or expensive to be useful.
Step 2: Train. Use the assessment results to prioritize training content. Start with the highest-risk behaviors and the highest-risk employees. Finance teams need wire fraud defense. HR teams need social engineering awareness around employee data. All employees need phishing recognition and password hygiene. Deliver training in short, frequent sessions rather than one long annual event. Research consistently shows that shorter, repeated sessions produce far better retention than a single long course.
Step 3: Measure. Track phishing simulation click rates, incident reporting rates, training completion rates, and the frequency of actual security incidents over time. According to the 2025 Security Awareness and Training Global Research Report, 67% of organizations report moderate or significant reductions in intrusions and breaches after implementing training. Measurement makes those improvements visible and helps justify continued investment. It also identifies employees who may need additional support before a real attack finds them first.
How to Do Security Awareness Training?
Security awareness training is done by following a repeating cycle of assess, train, and measure with several specific elements in place. Start with a baseline phishing test to set a starting point. Build a training curriculum that covers the three main areas: phishing and social engineering recognition, password security, and data protection. Deliver it in short sessions, ideally monthly micro-trainings of 10 to 20 minutes rather than a single annual course. Run regular phishing simulations throughout the year, providing immediate feedback and remedial training to anyone who clicks a test link. Establish a clear and easy way for employees to report suspicious activity, and recognize employees who report correctly. Review metrics quarterly and update content to reflect new attack techniques. For businesses that lack the internal resources to build and manage this themselves, managed security services can handle the entire program. Our Managed IT Department services include security awareness components built for your specific industry and compliance needs.
What Are the Most Important Areas to Focus On in Security Awareness Training?
The most important areas to focus on in security awareness training are phishing recognition, credential security, and data handling, in that order of priority. These three areas represent the most common human behaviors that lead to breaches, and the ones where training produces the most measurable improvement.
Beyond those three, the next priority areas depend on your industry and risk profile. Healthcare organizations should add training on patient data handling and HIPAA-specific scenarios. Financial firms should add business email compromise defense, wire fraud prevention, and FTC Safeguards Rule compliance. Government contractors must add controlled unclassified information handling and CMMC-specific security behaviors.
Across all industries, insider threat awareness is increasingly important. According to the 2024 Cybersecurity Insiders Insider Threat Report, 83% of organizations reported at least one insider attack in the previous year, and 48% said incidents had increased compared to the year before. Not all insider incidents are malicious. The majority come from negligent or poorly trained employees who do not realize what they are doing is risky. Training that addresses insider threat behavior, including how to recognize and report suspicious activity by coworkers, is a meaningful addition to any program. For a deeper look at how to audit and assess your current security posture, our post on the benefits of regular cybersecurity audits explains where training fits into the bigger picture.
What Are Examples of Security Awareness?
Examples of security awareness include recognizing a phishing email before clicking on it, using a unique password and enabling MFA on every work account, locking a computer screen when stepping away from the desk, verifying a wire transfer request by calling the requester directly through a known phone number, reporting a suspicious USB drive left in a common area rather than plugging it in, and noticing when a coworker accesses systems outside their normal role. Security awareness is visible in daily behaviors, not just quiz scores. A culture where employees feel safe and encouraged to speak up when something seems off is the clearest sign that training has worked.
What Are the Three Levels of Security?
The three levels of security are strategic, tactical, and operational. Strategic security is the high-level planning and policy-setting that happens at the leadership level. This includes deciding which compliance frameworks to pursue, setting the overall security budget, and establishing the organization's risk tolerance. Tactical security translates those strategies into specific programs and controls, like choosing which training platform to use, which compliance framework to target, or how to structure your incident response plan. Operational security is the day-to-day execution: running the phishing simulations, delivering the training modules, monitoring the network, and responding to incidents as they happen.
Security awareness training touches all three levels. At the strategic level, leadership must commit to funding and prioritizing training as a core security investment. At the tactical level, the training program must be designed to address the specific risks and compliance requirements of the organization. At the operational level, employees must participate regularly and apply what they have learned in their daily work. When all three levels are aligned, training delivers its full benefit.
What Are the 4 D's of Security?
The 4 D's of security are deter, detect, delay, and defend. Deter means making your organization a less attractive target through visible security measures. Detect means having systems and trained employees who can spot a threat early. Delay means slowing an attacker's progress through layered controls so there is time to respond. Defend means actively containing and stopping a threat before it causes full damage. Security awareness training contributes to all four. A trained workforce deters social engineering attempts, detects phishing faster, delays breach progression by reporting quickly, and defends the organization by following incident procedures correctly.
What Is the Triple D in Security?
The Triple D in security refers to Deter, Detect, and Defend, a simplified version of the security response model. Deter focuses on discouraging attacks through strong security posture and visible controls. Detect focuses on identifying threats that do get through deterrence. Defend focuses on actively responding to stop damage. Some frameworks also refer to the Triple D as Detect, Deny, and Delay, with a similar meaning. In all versions, security awareness training plays a role in detection by giving employees the knowledge to recognize threats, and in defense by ensuring they know what action to take when they do.
Frequently Asked Questions
What Are the Three Fundamental Goals for Security?
The three fundamental goals for security are confidentiality, integrity, and availability, forming the CIA triad. Confidentiality means keeping sensitive information away from unauthorized people. Integrity means ensuring data is accurate and has not been altered without permission. Availability means keeping systems and data accessible to legitimate users when they need them. Security awareness training supports all three: employees who recognize phishing protect confidentiality, employees who verify unusual requests protect integrity, and employees who respond quickly to ransomware attempts protect availability.
What Are the 3 DS of Security?
The 3 DS of security are deter, detect, and defend. Deter involves making your organization a harder target by having visible security controls and a trained workforce. Detect involves identifying threats early through monitoring tools and alert employees who know what to look for. Defend involves responding to active threats quickly and effectively to minimize damage. Security awareness training builds the human capacity for all three: trained employees deter social engineering, spot phishing faster than untrained staff, and follow incident procedures that limit how far a breach spreads.
What Are the Three Domains of Security?
The three domains of security are physical security, cybersecurity, and personnel security. Physical security protects facilities and equipment. Cybersecurity protects networks, systems, and data. Personnel security addresses the risks that come from people, including insider threats, access management, and security training. Security awareness training lives in the personnel security domain but connects directly to the other two. Trained employees support physical security by following access procedures and trained employees support cybersecurity by not clicking phishing links or using weak passwords.
What Are the Five W's in Security?
The five W's in security are who, what, when, where, and why. Who refers to identifying which users have access to which systems. What refers to the specific data or resources being protected. When refers to when access is granted or when an incident occurred. Where refers to the physical or network location of systems and data. Why refers to the reason a user needs access or why an incident happened. Security awareness training addresses all five W's by teaching employees to ask these questions before acting on a request. Employees who pause and consider the who, what, when, where, and why of an unusual email or instruction are far less likely to fall for social engineering.
What Are the 7 P's in Security?
The 7 P's in security are people, process, policy, physical, perimeter, protection, and purpose. People are the human element, which includes employee training and behavior. Process refers to the workflows and procedures that govern security activities. Policy sets the rules everyone must follow. Physical covers the hardware, buildings, and facilities. Perimeter refers to the network and digital boundaries that separate trusted from untrusted environments. Protection refers to the technical tools like firewalls and endpoint security. Purpose ties everything together by ensuring security measures are matched to the actual business risks and goals. Security awareness training addresses the first three P's directly and supports all seven by ensuring that people understand and follow the policies and processes that govern the others.
How Often Should Security Awareness Training Be Updated?
Security awareness training should be updated at least quarterly to stay current with evolving threats. The threat landscape changes fast. According to research from TitanHQ and Osterman Research, 64% of businesses expect phishing threats to increase, driven by AI tools that allow attackers to generate more convincing fake emails at scale. AI-powered phishing attacks improved from being 31% less effective than human-crafted emails in 2023 to 24% more effective by early 2025, according to Brightside AI's analysis of multiple studies. Training content that was accurate 12 months ago may already be outdated. Quarterly updates to include new attack techniques, current threat examples, and updated compliance requirements keep employees prepared for what attackers are actually doing today.
What Are the 4 A's of Security?
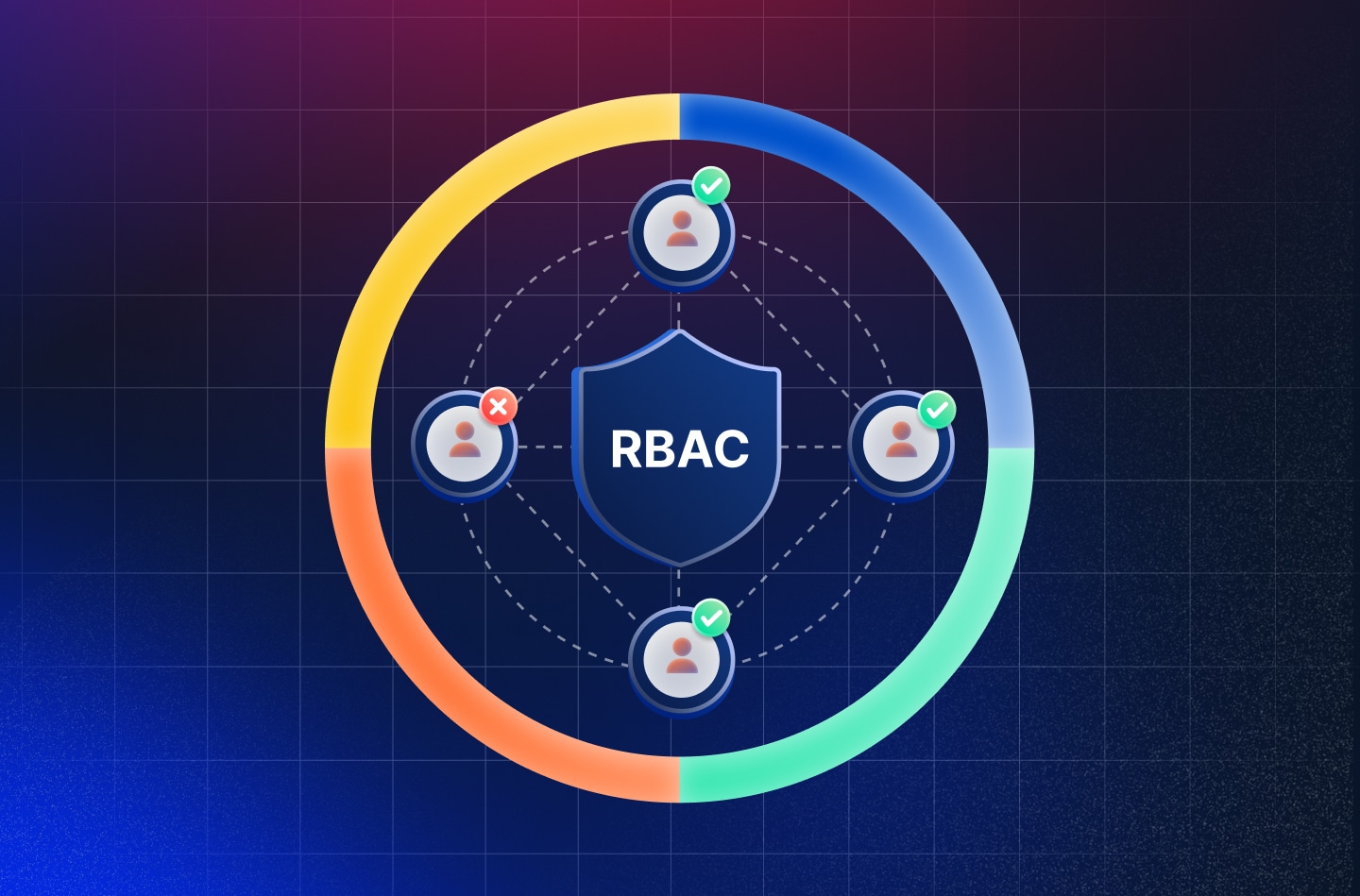
The 4 A's of security are authentication, authorization, auditing, and accountability. Authentication verifies who a user is before granting access. Authorization defines what a verified user is allowed to do. Auditing tracks and records what actions were taken and by whom. Accountability means users can be held responsible for their actions based on those records. Security awareness training directly supports authentication by teaching employees to use strong passwords and MFA, and it supports accountability by teaching employees to follow documented procedures that leave a verifiable trail. When employees understand why these controls exist, they are far more likely to comply with them consistently.
Putting It All Together
Security awareness training is not a one-time event. It is an ongoing process built around the three areas that matter most: phishing and social engineering recognition, password and credential security, and data protection with safe device use. When training covers these three areas consistently, with real simulations, short regular sessions, and clear reporting procedures, it produces measurable results. According to the 2025 Security Awareness and Training Global Research Report, 67% of organizations see moderate or significant reductions in breaches after implementing a proper training program. That number speaks for itself.
The organizations that struggle are the ones that treat training as a once-a-year checkbox. The ones that succeed treat it as a continuous habit, supported by leadership, measured by data, and reinforced through culture. Building that culture takes intention, but it does not require a large internal team. The right partner can run the program for you, keep the content current, and give you the reporting you need to satisfy compliance auditors and your own leadership.
If you are ready to build or strengthen your security awareness program, Interweave Technologies is here to help. Reach out through our contact page to schedule a free consultation with our team.
.webp)
.webp)





.webp)





Share Post